The fine folks over at NixCraft just put out a review of FreeBSD Mastery: ZFS.
Seems that the book suffers from a shortage of suck.

Feral Books for Feral People
The fine folks over at NixCraft just put out a review of FreeBSD Mastery: ZFS.
Seems that the book suffers from a shortage of suck.
I’ll be at the Farmington Hills Public Library for the mug.org meeting on 10 November 2015, talking about SSH.
The talk will be pretty much based on SSH Mastery, as you might expect.
Meeting starts around 6:30 PM.
The library throws us out at 9PM, at which point a bunch of us troop out to Red Lobster for dinner. You’re welcome to come too.
MUG talks are normally filmed and available on YouTube. But you really do want to fly in from your distant continent to see this talk in person.
I haven’t done a general update since June? Well, let’s give where things are at the end of September. Because it’s October, and for my whole career my status reports have always been behind, and I see no reason to change now.
FreeBSD Mastery: Advanced ZFS is underway. Right now it’s in Allan Jude’s capable hands, but Allan has this thing called a “day job.” Apparently when you’re the It should be out before the end of the year.
In the meantime I’m mining words for FreeBSD Mastery: Specialty Filesystems. It covers NFS, nullfs, NTFS, and even filesystems not beginning with N. (Can’t think of what those are offhand, but I’m sure there are some.)
Immortal Clay 2, or Kipuka Blues, is at the line editor. So I’m waiting on that.
I’m spending 60-90 minutes a day on a new project called “Butterfly Stomp Waltz.” This started as a short story but, well, things happened–mainly that the folks who read it demanded the rest of the story. (Those of you eager for the new nonfiction books: if I stop writing fiction, my tech writing speed plunges. So this is to your benefit too.)
I suspect the next tech books will be on PAM, then something on OpenBSD httpd/relayd. (I’d really like to see httpd ported to more operating systems before I do that book, though.) I do intend to head towards the FreeBSD jails book, but after spending a year on FreeBSD filesystems I feel a definite need to poke elsewhere for a while.
Two chunks of news on my tech books yesterday:
1) nixCraft’s Wendy Michele wrote a very nice review of FreeBSD Mastery: Storage Essentials. Apparently I need to send her a copy of the ZFS book (which I’m perfectly okay with doing).
2) BSDTalk 2^8 discusses FreeBSD Mastery: ZFS. Recorded at vBSDCon, my coauthor Allan Jude does a good job talking about the book. Fortunately, someone came into the room before they were quite finished, cutting the interview short before Will could ask “What was it like working with Lucas?”
Here’s two short stories I’ve just put out. I had a complete blast writing these. I think you’ll enjoy reading them.
Spilled Mirovar
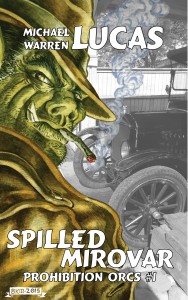
The modern year of 1927, and orcs still have to fight elven asshole bullshit.
Prohibition left exceptions for the church of Men, the Elvish sacraments, even the Dwarfish rituals. But the elves in Congress insist that orcs have no sacraments.
Without the Orcish draught, without the rites, Uruk-Tai’s fine strong boys might grow tall. They might earn respect.
But they will never be Orcs.
And Uruk will not let that happen…
Whisker Line
Snatched from the tunnels beneath his war-shattered homeland, Aleksander has everything he could want. The kind and generous people of the amazing New York City gave him a home. A job. A new leg. Teeth. Even a face.
He lives the perfect life—until bombs explode in the glass skyscrapers.
The fine people of New York don’t understand war.
But Aleksander and his secret Family do…
(Part of an intermittent continuing series on tech writing. People have urged me to write a book on how to write tech books for years. If I collect enough of these, I just might.)
I’m working on FreeBSD Mastery: Advanced ZFS, and am desperately hoping to have a first draft finished and out for tech review before my September writing workshop. And I’ve hit a situation I’ve hit many times before, but not in a way that will be so obvious to so many readers.
OpenZFS runs on many operating systems. FreeBSD is considered a Tier 1 OpenZFS platform, which is cool. But even so, not everything works quite the way you’d expect.
The current master document on tuning OpenZFS for better performance is Adam Leventhal’s article on the Delphix blog. The performance chapter needs to cover everything in that article and more, in a slower and more easily accessible manner.
But not everything on that blog post works on FreeBSD.
Some problems are straightforward to fix. The DTrace scripts are written for illumos, so some of them need minor tweaks to work on FreeBSD. I can ask around and get a knowledgeable kernel person to fix them (thank you, Ryan Stone!). Many parts need more explanation and context than Leventhal provides–which is great, because otherwise I’m out of a job.
But there’s the hard category: things that just don’t work on FreeBSD.
You can tune almost everything in ZFS, including how async writes perform. But the async tuning knobs are not useful without the speedometer that measures the impact of those changes on your hardware.
Performance tuning without measuring is not tuning: it’s voodoo. And not the voodoo religion that people sincerely practice, but the cheesy comic book thing that appears in any number of B movies when the filmmaker couldn’t be bothered to do any actual research.
The DTrace script that measures the effects of tuning async writes won’t work on FreeBSD. There’s a PR on this issue, but it’s sat there for three months now without anyone claiming it.
The Advanced ZFS book must address this. The issue for me isn’t so much the actual FreeBSD issue, but “how should the book address this?”
I could say any of the following.
Which is the correct path?
The first rule of writing a tech book is: serve your reader.
Or, as Mickey Spillane famously said, “I have no fans. You know what I got? Customers. And customers are your friends.” I must tell them the truth.
Number 3 is the easiest to write–just pretend it doesn’t exist. How many people actually need to tune async performance anyway? But the feature is in OpenZFS, and it’s fair for my readers to ask about it. Many readers will read my warnings about the feature, dismiss said warnings, play with async write tuning, and reluctantly concede that the warnings were correct.
Ignoring the matter is a disservice to my customers, so it’s out. As in so many things, the easiest thing to do is the wrong thing to do.
For most writers, in most situations, the correct answer is both #1 and #2. Admit the weakness up front. Don’t try to cover it up. State it flat-out for your readers:
“FreeBSD’s ZFS async writes are not as tunable as illumos’.”
Or, more accurately:
“Yes, you can tune FreeBSD’s ZFS async writes, but at the time I write this you cannot measure the effect of that tuning. So don’t do it. It won’t help most of you anyway. If you really must, look at this bug and study this blog post, if it’s still there.”
Yes, I’m a BSD guy. I’ve been a FreeBSD committer. I’m friends with a bunch of OpenBSD committers. I believe in the BSD philosophy–it comes straight out of my Boy Scout days. (Yes, I’m an Eagle Scout with the first palm, believe it or not!) I don’t want to diss any BSD, even in such a tiny matter.
But as a writer, it’s my job to speak the truth. (I’d argue this applies for all kinds of writing, not just tech writing, but it’s unquestionably 100% true for tech books.)
I could also take action before the book comes out, by using my influence as “the biggest BSD author” to whine at people until someone fixed it. Most authors don’t have that option, but I know these folks, and I could tag them all on Facebook until someone changed it. I could go to my fans and say “Fly, my flock! Fly to every FreeBSD developer you know, and throw this bug in their faces until they pay attention!”
But this method breaks my “don’t be a jerk” rule. (Yes, I have that rule. Shut up, Bob. And Warner! And–oh, fine, never mind.)
Another problem with this approach is, there might well be a very good reason why this patch isn’t merged. FreeBSD is not illumos. This apparently simple patch might to strange and terrible things to hosts in certain circumstances. Maybe it boosts latency or launches ICBMs at the nearest penguin sanctuary. I’m a writer, and totally unqualified to make this judgment.
Nevertheless, I’m going to try a little bit of the influence approach. Maybe I’ll write a blog post about the issue, hoping that someone of influence will see it. A few influential FreeBSD folks follow my blog. Perhaps someone with the necessary skills will take interest and either close the bug with an explanation or commit it.
(Me, passive-agressive? Moi? Never!)
We all know that sysadmins don’t get enough credit.
Someone cared enough to create Sysadmin Appreciation Day, which is very nice, except that the only people who know about it are, well, sysadmins. And we are really crappy at appreciating anyone, including ourselves.
So, over at Tilted Windmill Press, I’m having a sale. The coupon code SAD15 gets you half off of all individual ebooks.
This means you could get all 7 Mastery titles in ebook for $35.
The coupon does not work on the discounted 3-book bundle, nor on the tip jar. Because the bundle is already discounted. And getting a coupon on my tip jar just seems like it would annoy me.
Similarly, this offer isn’t available on other platforms, such as Kindle or Apple. It’s only on the TWP web site because I fully control it.
Offer expires at midnight on Friday 31 July EDT.
I will not repeat this in 2016. Because random sales are only effective if they’re random.
On Thursday, August 20, 2015, I’ll be joining the Livingston Country BSD User Group to present about ZFS.
There are no plans to record this talk. If you want to see it, you’ll have to show up. Or, as I’m proposing a very similar talk to Penguicon 2016, you might show up there instead.
I posted this on various social networking sites, but I should probably put it here too.
I’m in Scottsdale, AZ, this week, on family business. I have a couple readers in the Phoenix area, so I’m inviting them, and everyone else in the area, to join me for dinner on Friday night at the Roaring Fork at 6PM.
I should probably mention: while I’m issuing the invite, you get to buy your own meal.
KB suggested the Brat Haus, which looks nice–except that almost all the seating is outside. And I’m thoroughly convinced that the only reason Phoenix was built is because this is where the founders’ last camel died.
So, if you’re in the Phoenix area, show up. Tell me why my books suck. I’m used to it.
Yes, it’s July. But these updates are for June. Because I put off writing this post.
Initial reaction to “FreeBSD Mastery: ZFS” has been positive. I’m pleased that so many people like the book.
Work on “FreeBSD Mastery: Advanced ZFS” is underway. I want to get this book done soon. Soooon. Because I’m kind of sick of writing about a single filesystem. This book should be smaller than the first ZFS book, thankfully.
I’m spending an hour a day on the sequel to Immortal Clay, called “Kipuka Blues.” I expect to have a first draft finished in July.
I now have three Montague Portal stories available. The first one is free on all platforms now, as a loss leader. Not sure how well that will work–the market for short fiction is smaller than the long fiction market. My fiction page has links for various Amazon sites, iBooks, Kobo, and more.
If I want FM: AZ done soon, and I want KB done soon, why don’t I pick one and crank on it? Nonfiction pays the bills, so I can’t drop everything and work on fiction. If I only write tech stuff, though, the nonfiction words go dry. Writing fiction keeps the nonfiction spigot clear and flowing.
I’ve done 200,000 words of publishable writing in the first half of 2015. I’d like to make in an even half million for the year. That’s not ridiculous–if I maintained my January and February outputs for every month of the year, I’d hit a million words in 2015. We’ll see what happens.
And as far as my master plan for writing full time goes: it seems that the rebooted Star Trek gets a whole lot better about Season 3. The bald French dude is no Kirk, but he’s not all bad. I hear they did some followup series. I might check those out once I’m done.